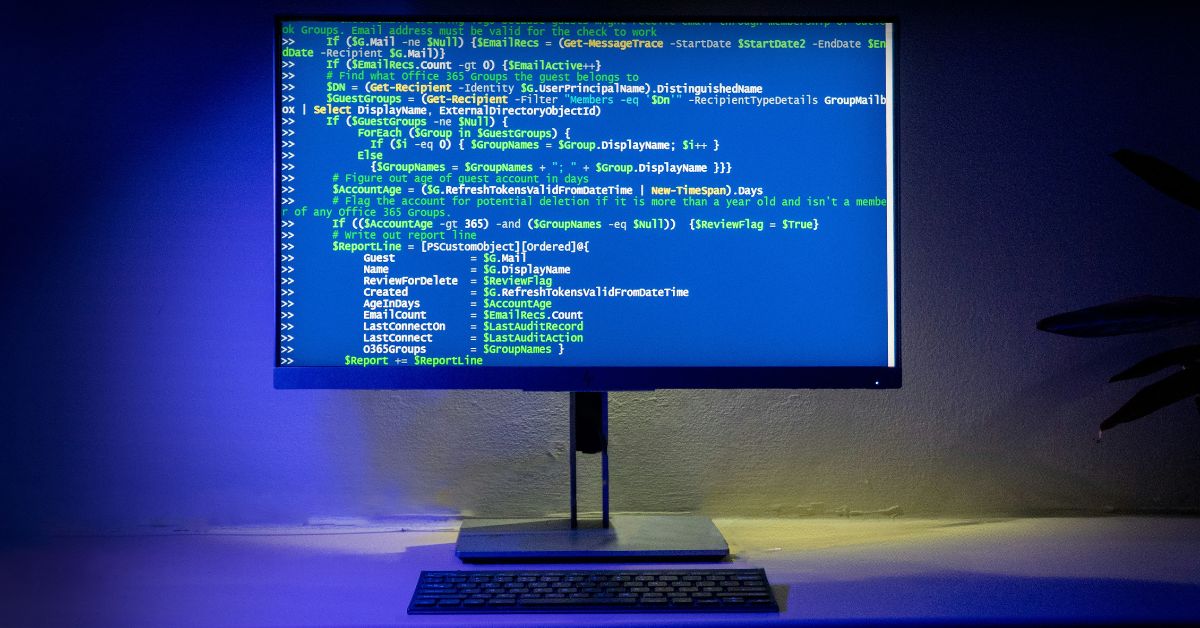
How Cybersecurity Impacts National Security
Cybersecurity is a top-tier national security priority because our nation’s critical infrastructure, economic stability, and the integrity of our state institutions are now all fundamentally dependent on a secure and resilient cyberspace. As of September 2, 2025, the nature of national power and conflict has been irrevocably altered. For a nation like Pakistan, with its…